Your AI Agents Should Be Getting Their Credentials from a PAM Vault

The rise of AI agents has created a problem that most security teams have not yet fully reckoned with. Developers are building agents that automate tasks, retrieve information, and take action on behalf of users. Those agents need credentials to do their jobs. And right now, in countless organizations, those credentials are being hardcoded into […]
Agentless vs. Agent-Based Security: Why Agents Are Obsolete

Enterprise networks are constantly evolving, driven by innovations in technology and the increasing need for efficiency, scalability, and security. One key debate in this evolution is the role of agent-based software in securing on-premises servers and workstations. Historically, agents played a vital role in enterprise IT, but as networks modernize, the necessity of these agents […]
The Importance of Dynamic Asset Classification in Privileged Access Management (PAM)

In this post, we explore the importance of dynamic asset classification for Zero Trust security.
How to Enable MFA Before RDP and SSH Sessions
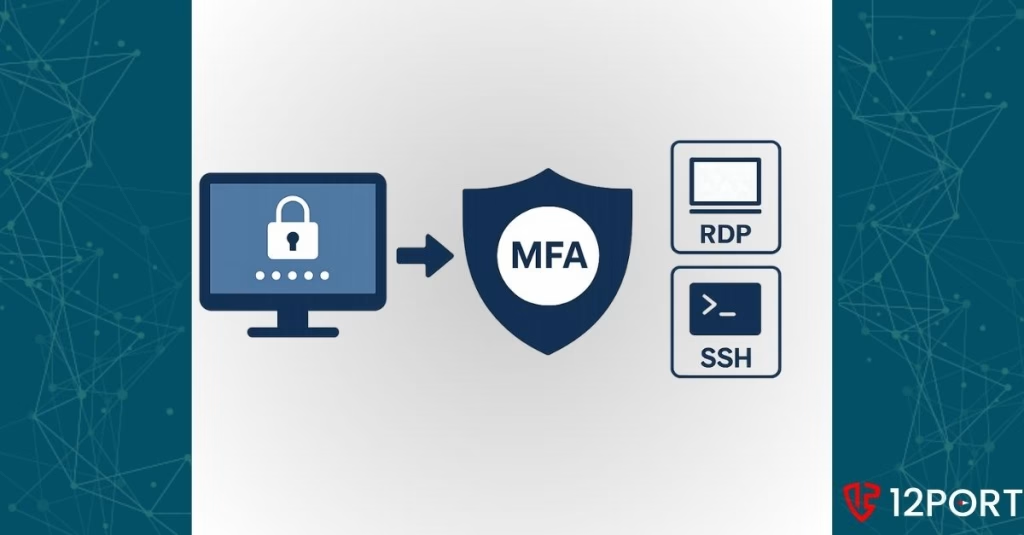
Remote access is essential for modern enterprises. IT administrators, DevOps teams, and vendors need to connect to critical infrastructure using Remote Desktop Protocol (RDP) or Secure Shell (SSH). But many organizations still allow these sessions without enforcing a critical security control: multi-factor authentication (MFA) before the session begins. MFA is a proven method to reduce […]