12PORT vs. DELINEA
One unified broker, not a Thycotic-plus-Centrify stack.
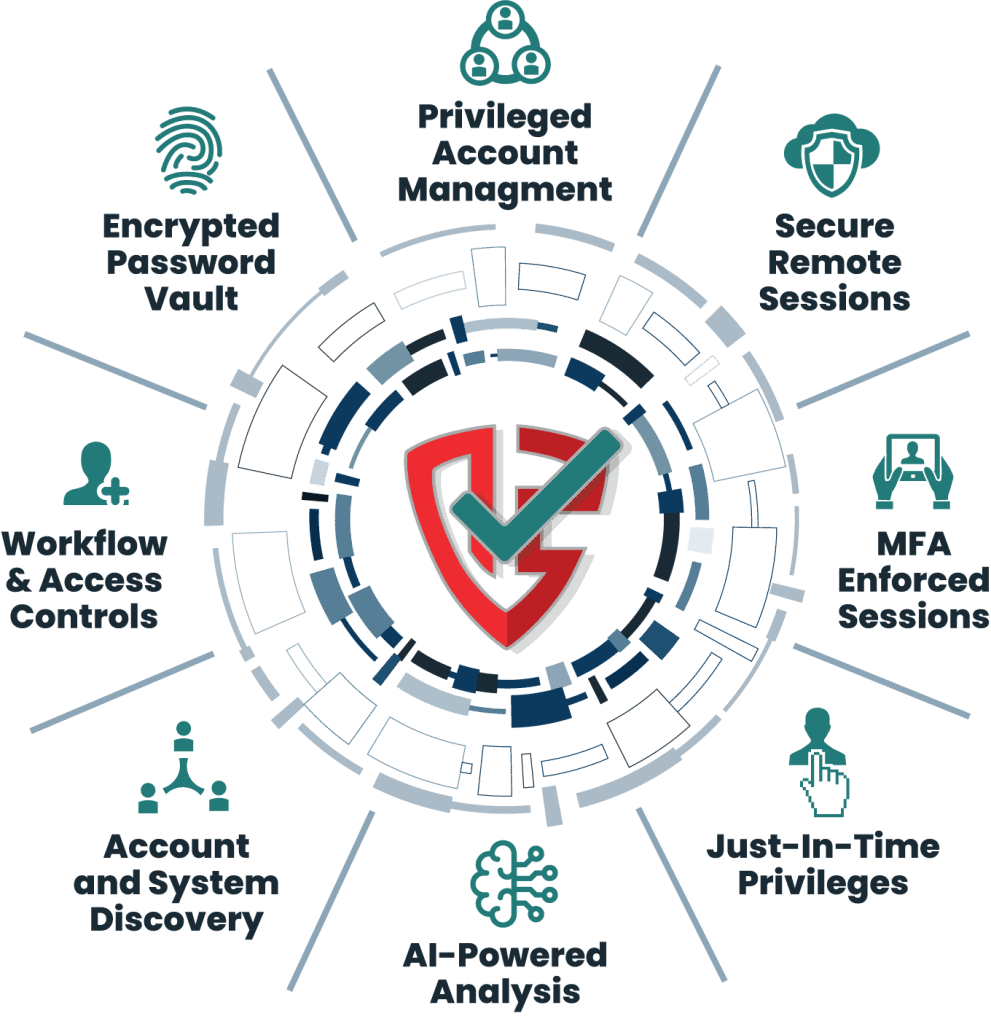
Delinea was formed by merging Thycotic (Secret Server, Privilege Manager) with Centrify (Server PAM). The product portfolio still reflects that history. 12Port covers vault, brokering, account management, recording, intelligence, and AI-agent access in a single platform. One console, one license, one architecture.
Architecture differences
What 12Port does differently than Delinea.
Delinea’s portfolio (Secret Server, Privilege Manager, Server PAM, Privileged Behavior Analytics) is the result of the Thycotic + Centrify merger. The platforms share a brand and a roadmap toward unification, but distinct UIs and licensing models still reflect their origins. 12Port avoids that complexity because it was built as a single product.
- Agentless brokering vs. Server PAM agents. Delinea Server PAM (the former Centrify product) requires agents on Linux and Windows servers for privilege elevation and gateway-less access. 12Port brokers SSH, RDP, PowerShell, VNC, Telnet, and HTTP(s) sessions through a server-side broker. No agents on the targets.
- One console, not Secret Server + Privilege Manager + Server PAM. 12Port covers vault, account management, brokering, recording, intelligence, and AI-agent access in one console. Delinea customers typically operate multiple admin UIs and integrate them with their own glue.
- AI agents authenticate to a native MCP server. 12Port’s MCP server lets AI agents request privileged actions through the same broker that humans use, with the same approval and recording. Delinea’s AI story is service-account secret rotation plus Privileged Behavior Analytics, not a privileged plane for agents.
- Multi-tenant by design. 12Port runs MSPs and multi-business-unit enterprises from one control plane with isolated tenants, per-tenant audit, and per-tenant reporting. Delinea Secret Server multi-tenancy exists but is layered on top of the original architecture.
Side-by-side
Delinea vs. 12Port at a glance.
| Capability | Delinea | 12Port |
|---|---|---|
| Endpoint footprint | Server PAM agents on Linux/Windows; Privilege Manager agent on endpoints | Agentless. Nothing on endpoint or target |
| Time to first session | Weeks to months (Secret Server install + Server PAM agent rollout) | Same day. Connect IdP, point at assets, broker |
| Product count | Secret Server + Privilege Manager + Server PAM + PBA = 4 SKUs | One platform, one license |
| AI agent support | Service-account model + PBA behavior analytics | Native MCP server. Agents authenticate and request like humans |
| Multi-tenancy | Layered on Secret Server; separate Server PAM tenants | Native, single control plane, isolated tenants |
| Session recording | Video + keystrokes (Secret Server, Server PAM) | Video + transcript + event log + plain-language search |
| Pricing model | Per-secret + per-server + per-feature; quote-driven | Per named user, all modules included; quote-driven |
| Deployment options | Cloud (Secret Server Cloud), self-hosted | On-prem, cloud, isolated networks. Same product |
Honest framing
When Delinea is the right answer. When 12Port is.
Delinea fits when…
- You already run a mature Secret Server deployment with deep integrations and a team trained on the Thycotic admin UI.
- You depend on Centrify Server PAM for Active Directory bridging on Linux servers and you don’t want to disrupt that pattern.
- Your security team has standardized on Delinea for compliance reporting in regulated environments and you have an active enterprise contract.
12Port fits when…
- You want one console, one license, one architecture, not Secret Server plus Privilege Manager plus Server PAM stitched together.
- You priced out a Delinea renewal or expansion and the per-secret + per-server + per-feature math does not line up with the privileged identities you actually have under management.
- Your Delinea rollout has stalled. It is common: agent rollouts on Server PAM, vault migration projects, and integrations across Secret Server + Privilege Manager + Server PAM cost more time and budget than expected, the original scope shrinks, and a meaningful slice of privileged identities never makes it onto the platform.
- You are heavily invested in Delinea for legacy systems but want a faster, cheaper path to bring new projects, acquisitions, cloud accounts, K8s clusters, and AI agents under privileged-access management, without rolling out Server PAM agents per workload.
- AI agents are part of your access plan, and you want them brokered through the same control plane as humans.
- You run an MSP or a multi-business-unit enterprise and need real native multi-tenancy, not separate tenant deployments.
- You want pricing that scales with how many people use the platform, not per-secret, per-server, per-feature.