PRIVILEGED ACCESS MANAGEMENT
Brokered Privileged Access. Zero Credential Exposure.
Agentless privileged access broker with credential injection, session recording, and full audit. Brokers SSH, RDP, PowerShell, VNC, Telnet, HTTP(s), and Kubernetes through a web client or through native desktop and mobile clients.
Stop credential-based attacks, enforce least privilege, and make every privileged action fully accountable.
How it works
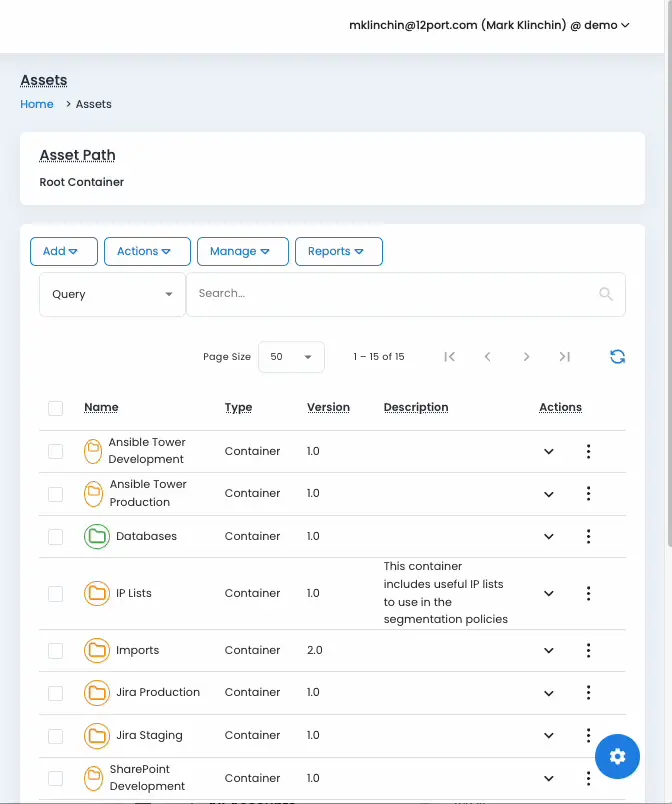
A single broker between every privileged identity and every system you protect.
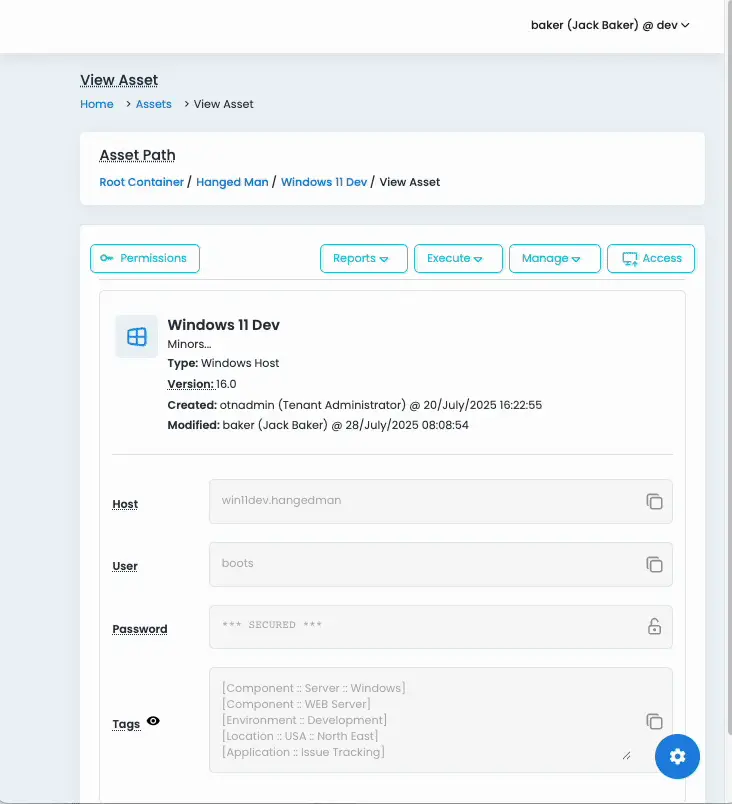
Operators, vendors, scripts, and AI agents authenticate to 12Port with their corporate identity. 12Port retrieves the target password or credential from the secured vault, opens an SSH, RDP, PowerShell, VNC, Telnet, or HTTP(s) session against the target system, and records everything that happens. Passwords, keys, and credentials are injected through the broker. It never reaches the user’s clipboard, the endpoint, or the device.
The broker is agentless and protocol-native, so 12Port can sit in front of any system that already speaks SSH, RDP, PowerShell, VNC, Telnet, HTTP(s), or Kubernetes. There is no software to install on the target, the endpoint, or the user’s machine.
Access broker
Brokered access. Protocols, endpoints, and controls.
Web client without agents
Brokers SSH, RDP, VNC, Telnet, and Kubernetes through 12Port’s web client. Records video, events, transcripts, file transfers, and clipboard activity. No agent on the endpoint or the target.
Adaptive MFA mid-session
Optional MFA enforcement on web and native clients — including session interruption when policy or behavioral signals require re-verification.
Web Portal access via HTTP(s)
Brokered HTTP(s) access to web consoles, with credential injection and session recording. No RDS infrastructure required.
Why it’s different
What 12Port’s access broker does that legacy PAM does not.
Agentless across the stack
No agent on targets. No agent on endpoints. No agent fleet to patch, certify, or audit. Targets just speak the protocol they already speak.
Single-entry enforcement
Optional centralized broker as the only entry point to network devices. Reduces attack surface, prevents lateral direct access, and gives you one audit trail across every protocol.
Distributed for isolated networks
Brokers reach into isolated cloud, datacenter, and on-prem networks separating data and control planes, without changing perimeter firewall rules.
Command and clipboard filter
Block file transfers, redact clipboard contents, and filter privileged commands (sudo, enable) per session policy. Audit shows exactly what was attempted.
Zero Trust to RDS apps
Brokers Zero Trust access to Windows desktop applications published via RDS Remote Applications: database clients, cloud consoles, mainframe terminals, and OT engineering tools.
Open and integrable
Customizable script library and full REST API. AI agents request access through an MCP server. SIEM integration and AI-Powered Analysis exposed end-to-end.
Enforcement
PAM that can’t be bypassed.
Vaulting protects credentials. AccessWall enforces access. With AccessWall, every privileged connection is routed through 12Port at the host level. Stolen credentials, shadow tooling, and direct SSH or RDP from an admin workstation all stop working outside the brokered path.
Your PAM controls become technically enforced, not advisory. No manual firewall changes. No per-host scripts. No agents on the protected systems.
See it in action
Inside the 12Port platform.
Click any tile to zoom in. Use the arrow keys or on-screen controls to step through.