CREDENTIAL VAULT
One vault for every privileged secret. Never disclosed to the user.
Service accounts, API keys, certificates, SSH keys, and database credentials are stored in 12Port’s secured vault. Just-in-time injection through the access broker. The credential never reaches the user’s clipboard, browser, or terminal.
Eliminate credential exposure and reduce risk across every identity.
How it works
Vault, broker, and audit. One workflow.
Operators, scripts, and AI agents authenticate to 12Port with their corporate identity. 12Port retrieves the target credential from the vault, opens the privileged session through the broker, and records everything. The credential is injected by the broker. The user never sees it, the endpoint never receives it, and the device never stores it.
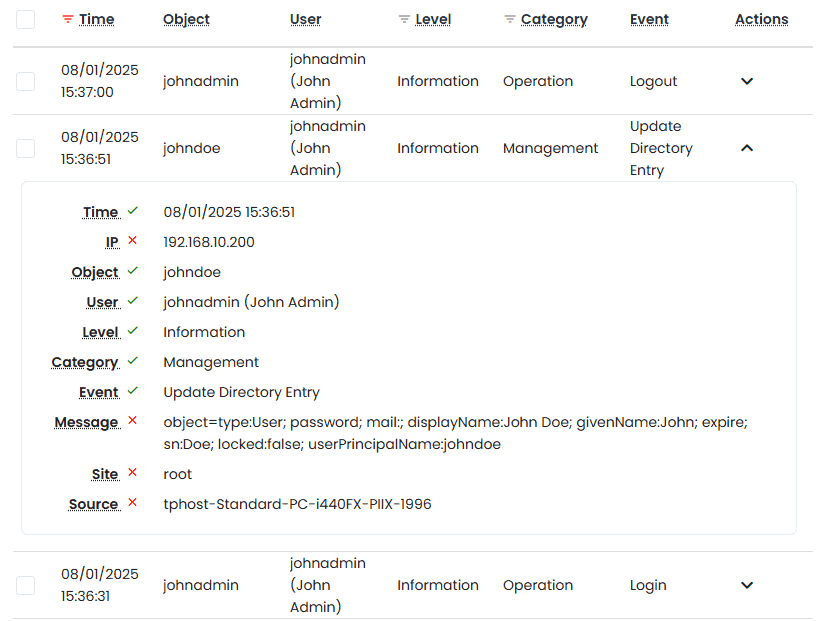
Every check-out, rotation, and access decision is recorded with full audit context: who requested, what target, which approval, when, from where. Split knowledge and dual control are available for the highest-sensitivity credentials.
Secured vault
Every secret. One vault. Full audit.
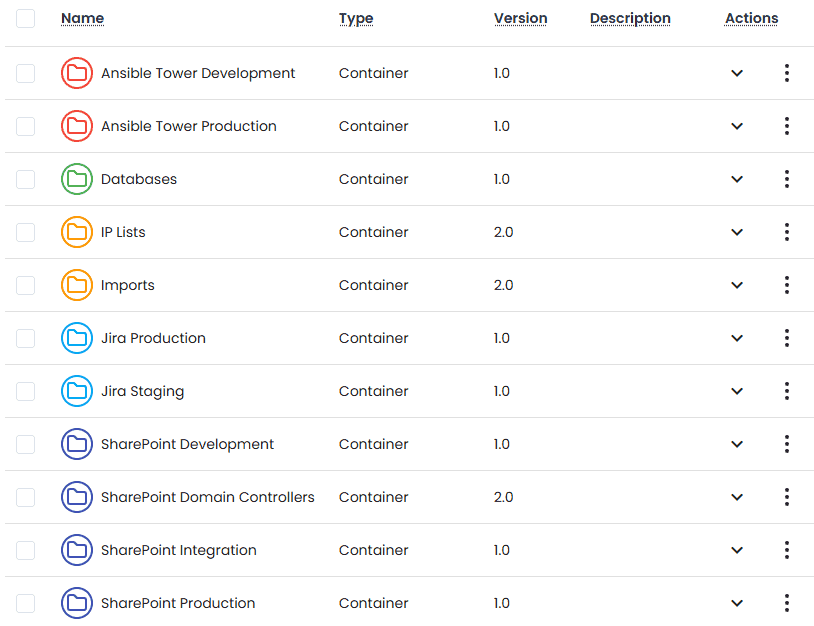
Service accounts & API keys
Centralized vaulting for service accounts, API keys, OAuth tokens, and machine credentials. Rotated on schedule or on event.
SSH keys & certificates
Public and private SSH keys, X.509 certificates, and signing keys. Discovered automatically. Rotated, reconciled, and never written to disk on the endpoint.
Database credentials
PostgreSQL, MySQL, SQL Server, Oracle, MongoDB. Native or AD-integrated. Brokered through a JDBC/ODBC-aware proxy with full query-level recording.
Cloud & SaaS identities
AWS, Azure, GCP root and service identities. Office 365, Salesforce, GitHub, Atlassian admin accounts. Vaulted, rotated, and brokered through SSO.
Why it’s different
A vault designed to never disclose.
JIT injection through the broker
Credentials are checked out at the moment of session establishment, used by the broker, and discarded. The user never sees the password. No copy-paste, no exposed tokens.
Split knowledge & dual control
High-sensitivity credentials can be split across two operators or require dual approval before release. Available per credential, per role, per target.
Auto-discovery
Discovers privileged accounts on Windows, Linux, Kubernetes, network devices, and databases. Brings them under management without an inventory project first.
See it in action
Inside the 12Port platform.
Scroll the row, then click any tile to zoom in.